Why These Pillars Create a High Bar — And Why Many Firms Struggle
Taken together, these five pillars impose stringent operational, technical, and governance requirements: full visibility of ICT assets and dependencies; continuous risk assessments; frequent testing; strong third-party oversight; coordinated incident management; and collaboration across the industry.
For many financial services organisations — especially those with hybrid infrastructure (on-prem + cloud), multi-vendor networks, legacy and modern systems, and outsourced dependencies — this is a significant compliance and operational challenge.
Common difficulties include:
- Fragmented knowledge of network topology and dependencies
- Partial visibility (some systems monitored, others opaque)
- Disjointed tools across cloud, network, on-prem, vendor, legacy
- Manual or static documentation, which becomes stale quickly
- Lack of ability to reliably simulate failures or verify all possible interdependencies
In short: traditional tools and practices often fall short of what DORA demands — and more
importantly, what auditors and regulators will expect now that enforcement is a real possibility.
What This Means for Resilience Strategies
Given DORA’s scope and complexity, a compliance strategy must include a unified, continuously updated view of the entire ICT estate — not just servers or applications, but also network connectivity, segmentation, cloud links, third-party connections, hybrid links, remote access, and more.
It must enable:
- Real-time visibility into what systems exist, where, and how they are connected
- Verification that configurations (routing, firewall, ACLs, segmentation) genuinely match documented security policies
- Automated evidence of infrastructure state and change history for audits
- Scenario and failure testing — including network failures, cloud region outages, third- party service disruption, and more
- Inclusion of third-party infrastructure in risk and resilience assessments
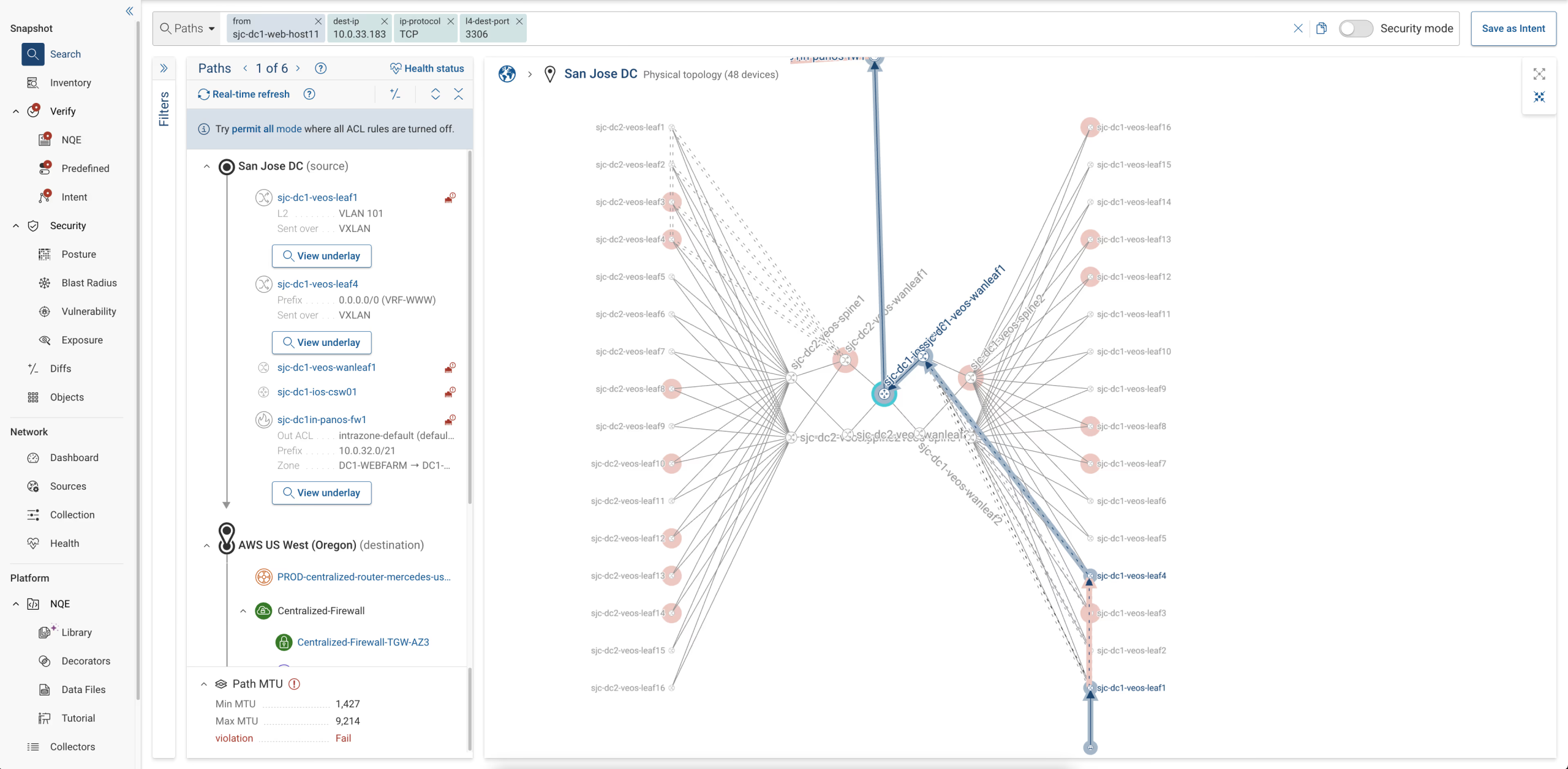
- Rapid root-cause analysis and incident reporting with full traceability of network paths and dependencies
Only with this sort of holistic visibility and behavioral verification can an organization realistically satisfy all five of DORA’s pillars — without creating unmanageable operational overhead.
Digital Twins and Digital Resilience:
Why the Financial Sector Needs a New Approach
As financial institutions face unprecedented operational-resilience expectations under DORA, many are discovering a fundamental issue: traditional tooling cannot deliver the unified, accurate, continuously updated view of ICT infrastructure that the regulation implicitly demands. Modern financial networks have become too complex — too hybrid, too interconnected, too dynamic — for manual documentation, scattered inventories, or siloed monitoring systems to keep pace.
This is where network digital twin technology is emerging as a transformative category.
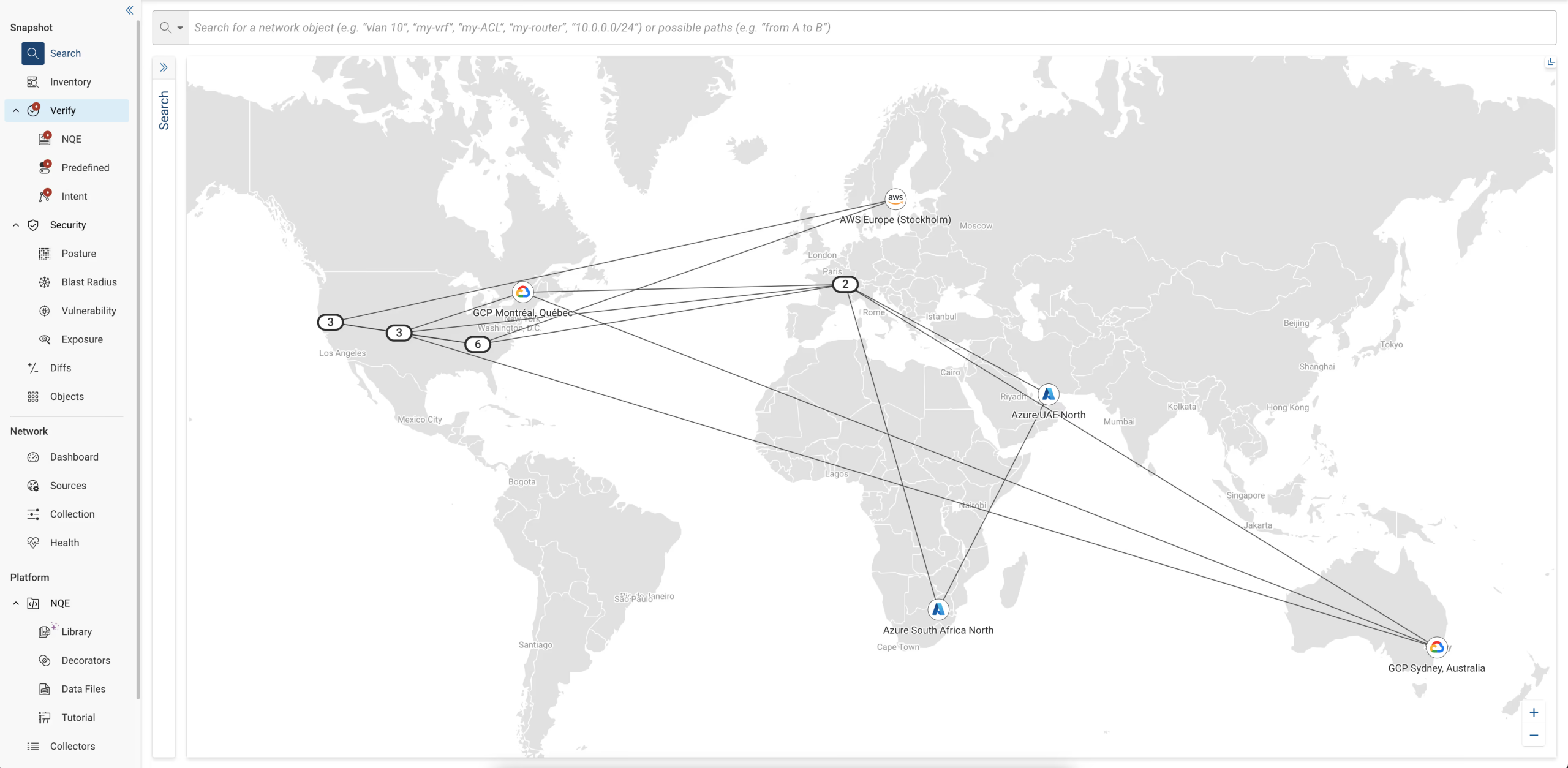
At its core, a digital twin is a mathematically accurate, continuously synchronized model of an institution’s end-to-end network and connectivity — across data centres, public cloud, hybrid environments, and third-party integrations. Unlike conventional mapping tools that rely on snapshots or polling, a true digital twin computes all possible behaviour of the network: every path, every rule, every control, every dependency.
For financial-services firms navigating DORA, this model offers a powerful foundation for compliance because it enables:
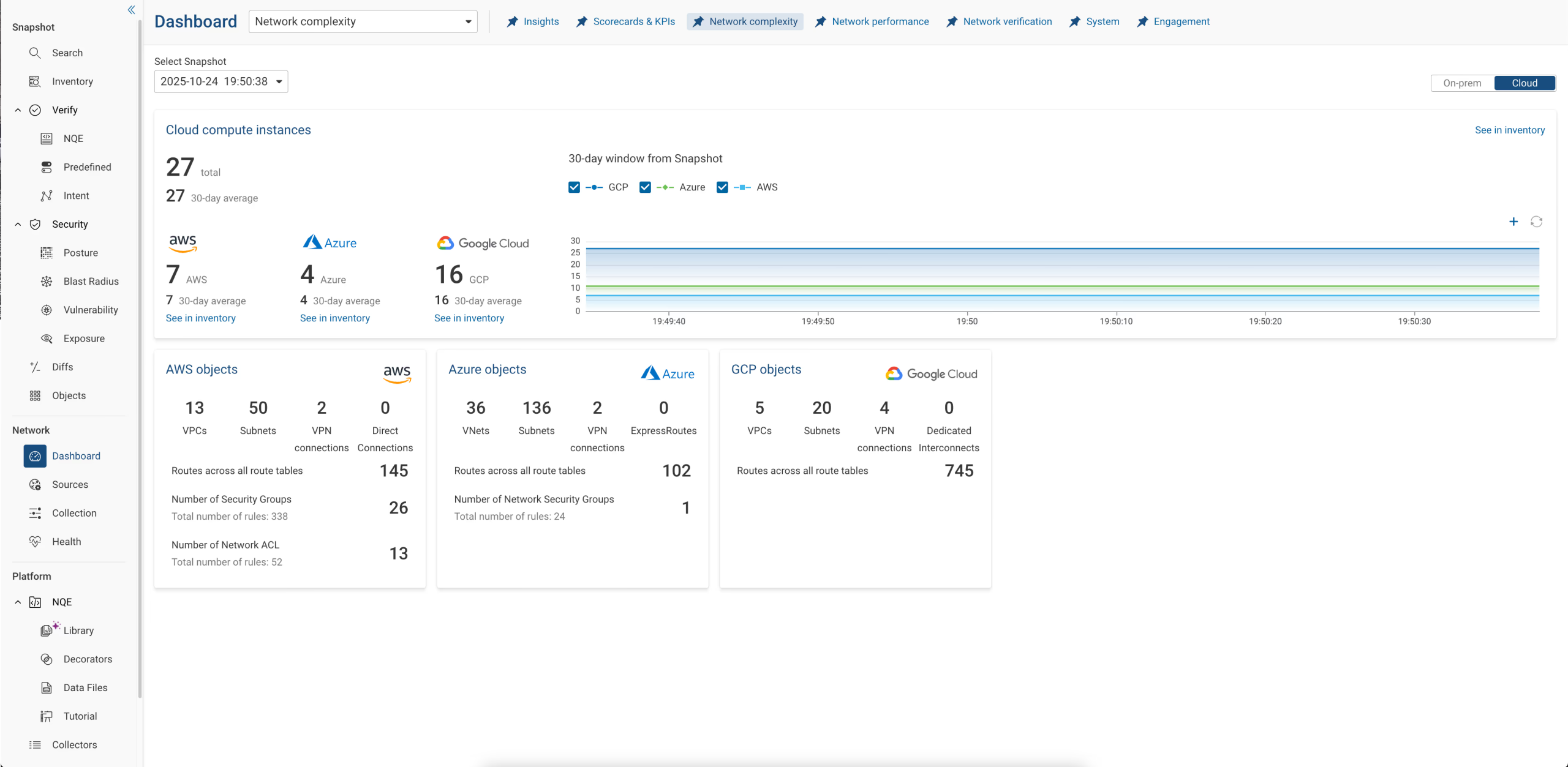
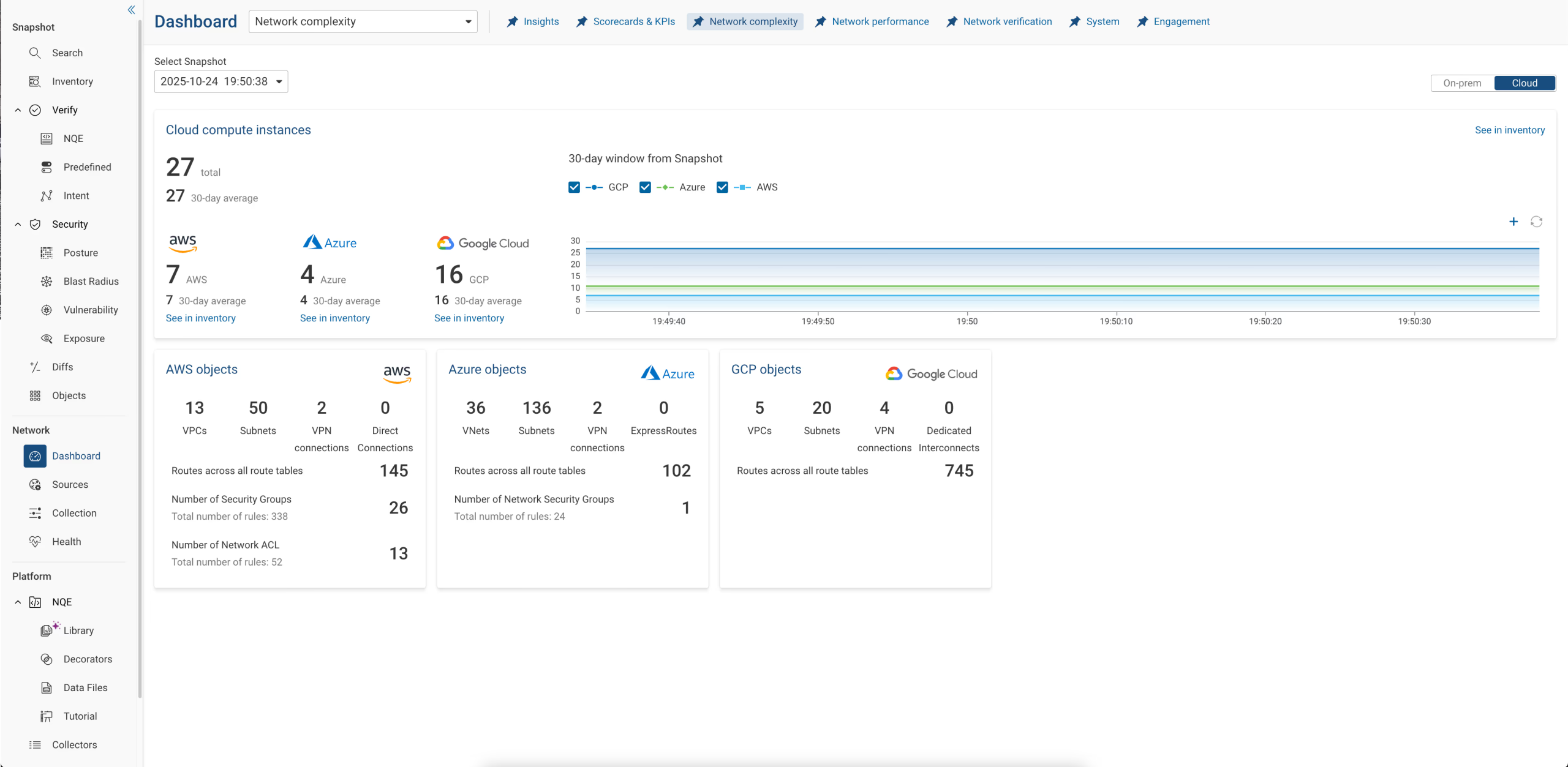
- Unified visibility across on-prem, cloud, and third-party ICT assets
- Accurate dependency mapping needed for critical-function identification and risk assessments
- Immediate detection of misconfigurations, inconsistencies, policy drift, and exposure paths
- Reliable incident analysis, root-cause identification, and regulatory reporting
- Continuous verification, simulation, and resilience testing without disrupting production
But it’s important to acknowledge a key point. Not all “digital twins” are equal, and many tools marketed as twins are simply automated diagrams.
For a digital twin to genuinely support DORA, certain capabilities are non-negotiable:
- A mathematically precise behavioural model, not just a topology drawing
- The ability to ingest, normalize, and reconcile multi-vendor, multi-cloud, hybrid configurations
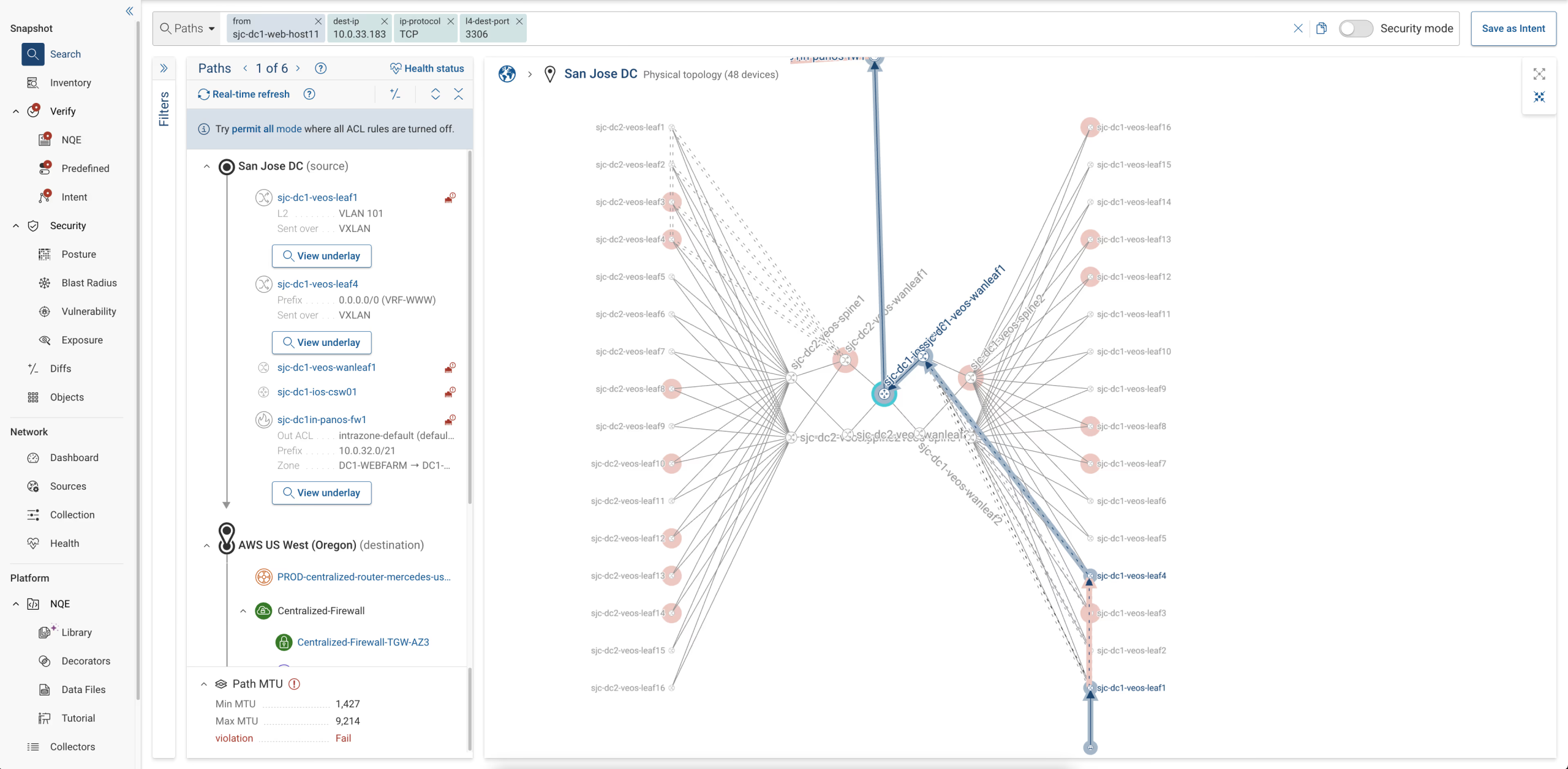
- End-to-end path computation reflecting actual forwarding logic, policy, and segmentation
- Full, historicized visibility for evidence, auditability, and change tracking
- Scalable support for enterprise-grade networks, architectures, and governance
This is the category that Forward Networks pioneered — long before DORA came into effect. The result is a technology stack that aligns unusually well with the regulation’s core expectations because it was designed to solve the underlying operational-resilience problems that DORA is now forcing firms to address.
How Network Digital Twins Fulfill DORA’s Core Requirements
…and Why Forward Networks’ Model Is Uniquely Aligned
DORA’s five regulatory pillars impose a level of infrastructure transparency, behavioural accuracy, and evidence-driven assurance that traditional tooling struggles to meet. A mathematically precise network digital twin — the type pioneered by Forward Networks — addresses these demands not by adding more dashboards, but by creating a single source of technical truth that reflects exactly how the ICT estate behaves at any moment in time.
Below, we map the capabilities of a true digital twin to the requirements within each DORA pillar.
1. ICT Risk Management (Articles 5–16)
DORA expects financial entities to maintain a comprehensive, continuously updated understanding of their ICT environment — including configurations, security controls, and interdependencies — and to ensure these are “consistent, complete, and functioning as intended.”
A digital twin supports these requirements by:
- Normalising and unifying configurations across vendors, clouds, and on-prem infrastructure
- Computing actual behaviour, not assumed behaviour — revealing unintended access, policy drift, or misrouting
- Highlighting deviations from internal standards or “golden configurations”
- Enabling continuous, automated checks aligned with internal control frameworks
Instead of discovering issues during audits or outages, institutions gain a live, verifiable risk-management baseline.
2. ICT Incident Reporting (Articles 17–23)
DORA mandates timely, detailed, technically accurate reporting for major ICT incidents — including root cause, affected assets, impact scope, and propagation paths.
A behavioural digital twin enhances incident reporting by:
- Providing instant blast-radius analysis: which systems were reachable, exposed, or impacted
- Reconstructing network behaviour before, during, and after the incident through historic snapshots
- Offering precise dependency insights that underpin root-cause identification
- Reducing investigation time so firms can meet the mandated reporting windows
This shifts incident reporting from manual reconstruction to evidence-based analysis.
3. Digital Operational Resilience Testing (Articles 24–28)
DORA requires continuous testing, scenario simulations, configuration reviews, penetration testing support, and examination of critical functions under failure conditions.
A digital twin enables this by:
- Mapping all dependencies and communication paths involving external providers
- Showing cloud and hybrid connectivity, including security groups, gateways, and firewalls
- Revealing unintended exposures or overly permissive connections to or through third-party systems
- Allowing firms to demonstrate to regulators exactly how third-party traffic is governed
This moves third-party assurance from contractual oversight to technical verification.
5. Information Sharing (Articles 34–36)
DORA encourages structured, evidence-backed information sharing among financial entities, especially around threats and vulnerabilities.
A digital twin supports this by:
- Providing a clear, vendor-neutral technical representation of affected paths or assets
- Enabling consistent reporting of misconfigurations or vulnerabilities across teams
- Reducing ambiguity by grounding conversations in the same canonical data model
This strengthens cross-institution coordination during cyber or operational events.