

-
partnerships

-
Recognized by Gartner®

In March 2024, the US Department of Defense (DoD) strategically shifted its network defense paradigm from a static, compliance-based inspection model (CCRI) to a dynamic, risk-focused Cyber Operational Readiness Assessment (CORA). This change mandated continuous, threat-informed cyber resilience, further rendering formerly manual audit preparation inadequate and inefficient.
This whitepaper asserts that modernizing the Department of Defense Information Network (DODIN) cyberdefense requires a novel technological leap. The Forward Enterprise Digital Twin Platform provides the continuous visibility and predictive risk modeling capabilities necessary to meet CORA audit requirements. By automating STIG compliance verification and viewing realworld threats using the MITRE ATT&CK framework, the digital twin allows DoD entities to move beyond reactive readiness to a state of proactive, measurable, and mission-aligned cyber defense, ensuring success in a short-notice CORA environment.
FROM CCRI TO CORA: THE END OF “CHECK-THE-BOX” COMPLIANCE
The previous Command Cyber Readiness Inspection (CCRI) model was popularly perceived by network operators as a compliance exercise. Its primary focus was auditing adherence to Security Technical Implementation Guides (STIGs), often resulting in a static, point-in-time test. This approach proved insufficient against sophisticated, Advanced Persistent Threats (APTs) and lacked the agility to accurately measure operational security.
THREAT-INFORMED DEFENSE: CORA’S FOCUS ON MITRE ATT&CK AND OPERATIONAL READINESS
The Cyber Operational Readiness Assessment (CORA) now serves as the DoD’s modern framework for evaluating a unit, base, or command’s genuine cybersecurity posture across the various components and networks that comprise the IT infrastructure. It represents a critical strategic shift, moving from mere administrative compliance to mission resilience and DODIN Defense.
Key Pillars of the CORA Framework:
The threat-informed nature of CORA demands a capability that eliminates the need for the manual, weeks-long “assessment crunches” that can cripple network teams’ productivity. The Forward Enterprise Digital Twin provides the foundational architectural capability for this continuous, proactive defense posture.
CONTINUOUS READINESS: AUTOMATING STIG COMPLIANCE AND CONFIGURATION VALIDATION
Traditional CORA preparation is resource-intensive, requiring network teams to spend countless hours manually querying and validating device configurations.
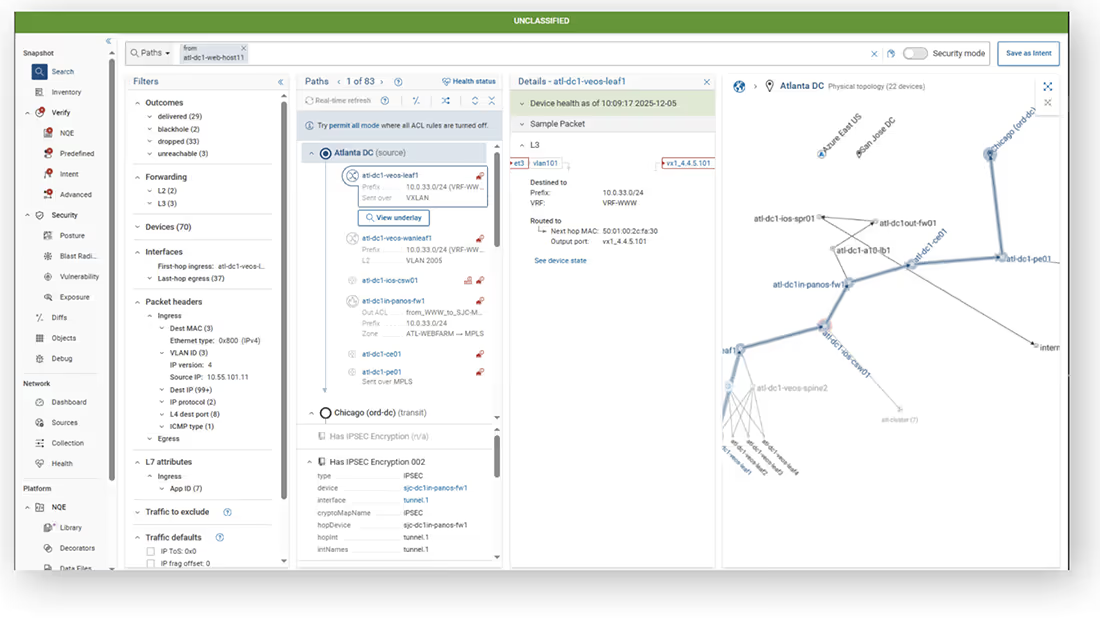
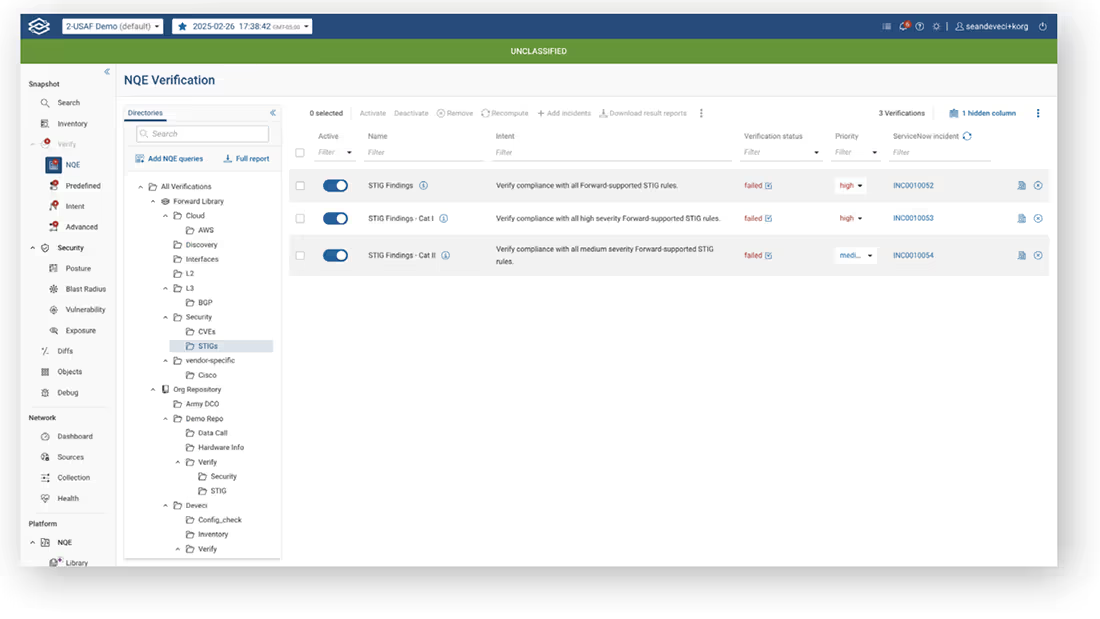
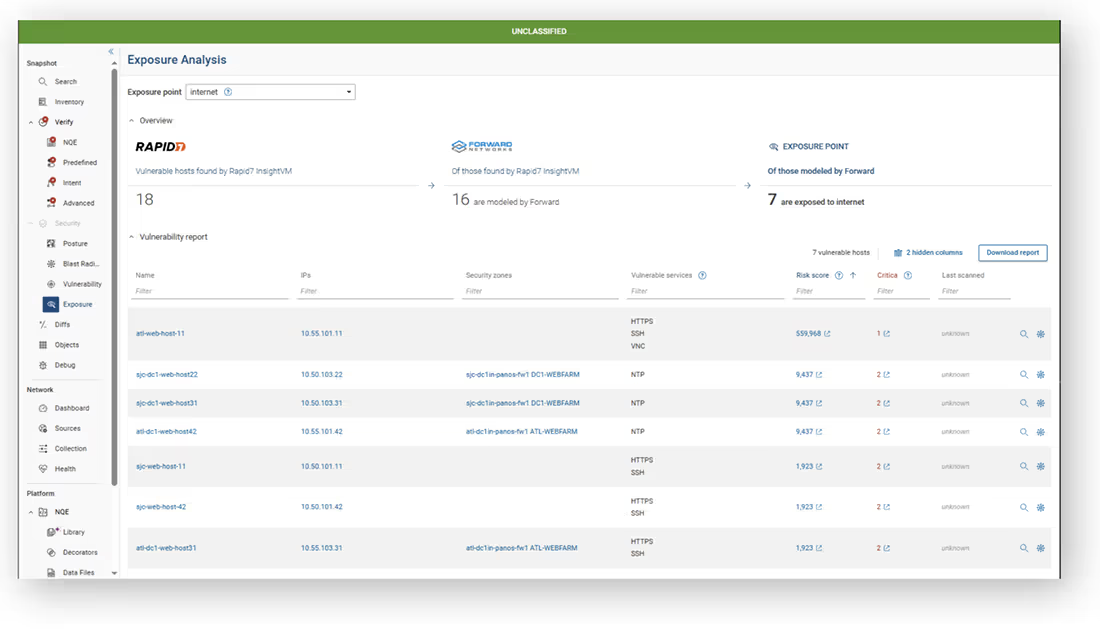
Automated Monitoring & STIG Compliance Validation: Forward Networks collects data from the live network, providing a near-time, “single pane of glass” view. The platform automates the validation of all network configurations, security policies, and compliance with directives (STIGs, FRAGOs, CTOs). This makes maintaining continuous readiness vastly simpler for a DoD entity.
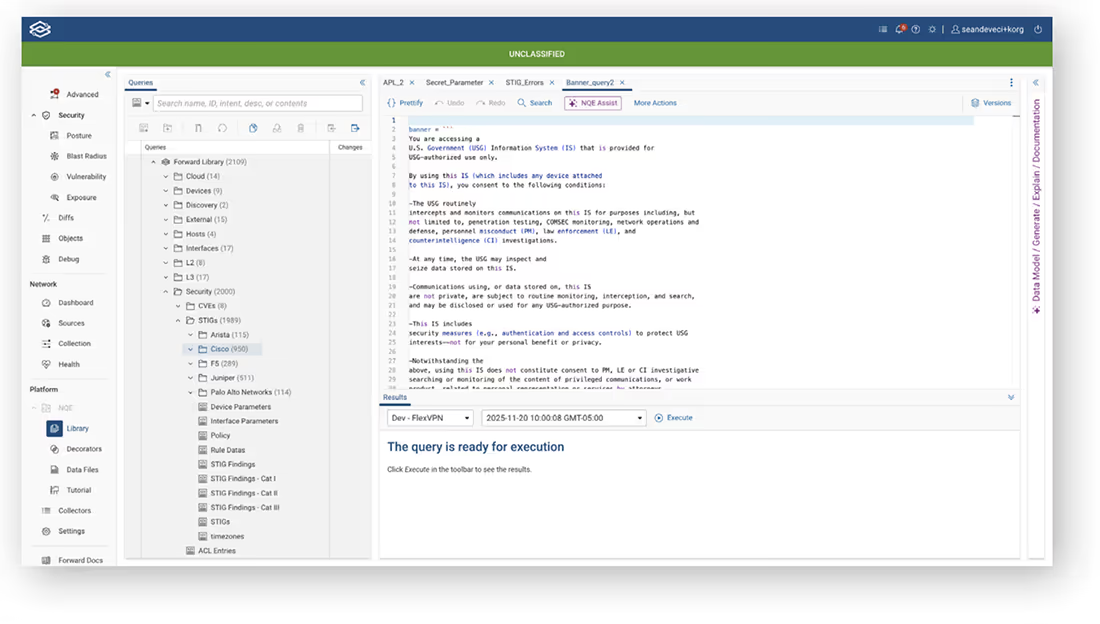
The Network Query Engine (NQE): The Forward Enterprise Network Query Engine (NQE) acts as an “independent targeting system” for compliance. It retrieves the full configuration and state of every device using native show commands, runs the files through a mathematical model, and instantly indexes the data. This allows teams to run customized checks to detect noncompliance and configuration drift with every snapshot, alerting them only if a violation is detected.
DYNAMIC RISK MODELING: SIMULATING THREATS WITH MITRE ATTACK
CORA prioritizes mitigation based on actual risk to the mission, requiring commanders to visualize and prioritize vulnerabilities based on how they enable an adversary’s TTPs.
NETWORK CHANGE ASSURANCE AND CONFIGURATION DRIFT CONTROL
The network is a living, breathing organism. Every change carries the risk of inadvertently impacting the CORA STIG score or introducing a security gap.
STREAMLINED CORA REPORTING AND AUTOMATED ARTIFACT GENERATIO
A primary pain point of a short-notice CORA is the scramble to generate the necessary artifacts and documentation. Automated Artifact Generation: With Forward Networks, a large portion of the required data for an assessment can be generated automatically. This significantly reduces the time and resources spent on manual data collection and reporting, making short-notice CORAs much less disruptive.
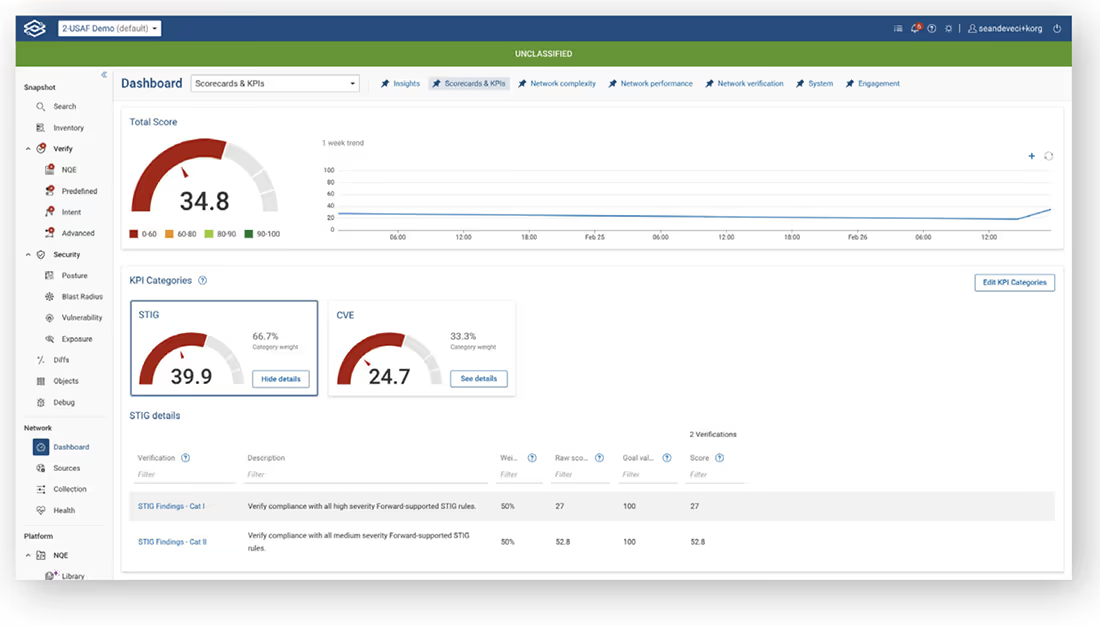
Centralized Source of Truth: The platform acts as a single, authoritative source of truth. Results can be shared via: .ckl file download for direct upload to compliance applications. Sharing a secure URL attached to tickets, providing the recipient with the exact same view for quick and informed remediation. Scorecard and KPI Dashboard: You can utilize the platform’s Scorecard and KPI dashboard to track metrics over time, adding weighted scores for each metric to visualize the score increase and demonstrate continuous improvement to assessors.
Training and Education: The digital twin also serves as a safe, virtual training environment for cyber defenders to practice incident response and learn about the network’s vulnerabilities without impacting the live system.
The Cyber Operational Readiness Assessment is the DoD’s commitment to genuine cyber resilience and mission assurance across the DODIN. Success in this new era requires moving beyond brittle, manual processes and embracing strategic network automation and validation.
The Forward Enterprise Digital Twin Platform, with its continuous NQE-powered validation, dynamic risk modeling, and change assurance capabilities, is not solely a network audit preparation tool—it is a strategic enabler for the DoD. It provides the decisiveness, efficiency, and continuous visibility needed to transform CORA preparation from a resource-draining scramble into a validated, day-to-day operational status, ensuring the network is always in fighting shape and aligned with the mission.